Documentation
Features
Security
What about framework security?
Today, creating a website without thoroughly paying attention to avoiding the techniques used by attackers is like leaving your house doors open at all time. It's an invitation to have your site defaced, you information stolen or, worse yet, your customers' data. It's giving anybody an opportunity to blow your reputation.
toKernel has been designed with security in mind and avoids the older PHP features that present security flaws or weaknesses. For example, we do not use any global variable such as 'global $db;' and for your addon development you do not need to include any file! Just write $this->lib... to access libraries and $this->app to access application functions.
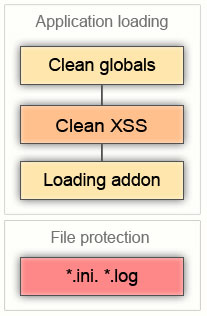
The method clean_globals is enabled by default. All global arrays are filtered, slashes stripped, etc... and the method 'clean_xss' is called on all data received.
In the toKernel framework, it is not possible to access the $_GET superglobal array. We make sure it is empty. Just call:
$this->lib->url->params('my_param');
to get data parsed from the url.
Access to all configuration and language files (.ini) and log files (.log) is restricted too.
While the framework security is our responsibility and concern, should you like to write any specific addon, you would however remain responsible for checking all sql and xss attack possibility in your code.
But to relieve and help you, we provide extensive guidelines on how to apply the best practices that would ensure your code is safe from malicious attacks. And we provide tools, such as the 'filter' and 'valid' class libraries, to make this task easier and faster, since we know that one of the main cause for security holes is the programmers lazyness or lack of time when confronted to tedious verification tasks.
